Nerd Chicks love a happy ending. Cliff hangers at the end of our favorite TV shows drive us nuts. After last weeks discussion of types of cyber bullying and the ways our kids are at risk, you may have been left thinking, ‘Ok, now that we’re sufficiently concerned, what’s a parent to do?’ Never fear, this week we’re exploring ways to reduce the risk that your child will become a victim of cyber bullying.
Disclaimer time: you know your kids and your family best. Some parents may be comfortable with a more hands off approach involving open communication with a trusted child, while others may need a little more control. We’re here to present some options to help you decide the path that’s right for your family. The main components to protecting any child are communication and education. Teach your kids to be vigilant about protecting their private information. Check out Stop Cyber Bullying to read about the ways cyberbullies target victims and how to get help if you think you’ve been a victim. There’s even a quiz to help kids determine if they’re unwittingly engaging in activities that may be victimizing others. If you don’t find all you need there, Wired Safety and Netsmartz and are great sources of Internet safety information.
E-Mail and Social Networking Sites: Anyone can create an email address and the person’s identification is rarely verified. Make sure your kids know not to open emails from unknown senders, even if the name looks familiar, and to be especially wary of attachments. Make sure they never share their passwords with anyone but you. Set your child’s Facebook or Twitter account privacy settings at the highest possible security level to prevent private information from being shared unintentionally and publicly.
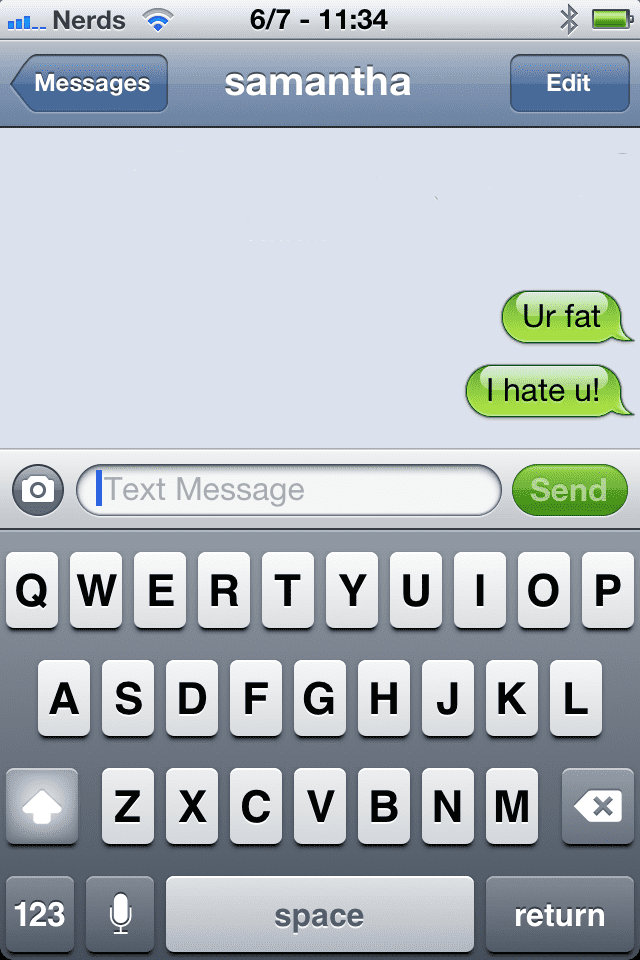
Cell Phones: Talk to your kids about “sexting” and the inherent dangers in participating. It can be illegal, images can be used against them by a bully, and it may affect their scholastic future. Encourage them to talk to you if they ever receive a text or picture message that makes them uncomfortable. Research shows that when parents are involved in their kids’ activities they’re less likely to engage in these behaviors. Whether that means limiting their per-month texting allowances or monitoring the texts and pictures they receive, let your kids know that limits you set are to help protect them.
Online Gaming: People who don’t “game” don’t realize how socially intimate the experience can be. Ask your children about their gaming experience like you ask about their day at school, specifically their interactions with other players. If you sense that they’re forming a close relationship, treat that person like you would any new friend. What do you want to know about that person to protect your child from a possible threat? If you suspect your child is being threatened or bullied by someone, contact the game administrators and report the abuse. In many instances, players can be banned for such activities.
Instant Messaging (IM): IM accounts can be acquired anonymously. Review your child’s buddy list for unknown contacts and talk to him or her about the identities of the people on their list. Learn as many of the chat acronyms as you can, such as POS (parent over shoulder) and A/S/L (age/sex/location) so you’ll be aware of anyone saying anything inappropriate to your child.
How do you know if your child is being bullied? They may avoid the computer, cell phone, and other technological devices or appear stressed when receiving an e-mail, IM or text. They may withdraw from friends or family, or be reluctant to attend school or social events. If you suspect your child is being bullied, trust your instincts.
Finally, you have technology on your side. We’ve detailed parental control and monitoring software in the past, but Spector Pro 6.0 is the best solution for parent that suspect their child may try to circumvent parental controls or monitoring if they are aware of them. It runs silently in the background so that no one but you will know it’s installed. It documents every keystroke, website visited, e-mail sent and received, chats and IMs. Everything they do on Facebook, including if they’re maintaining multiple accounts, will be captured. It may even provide you with the proof you need to report a bully to their ISP, their school, or higher authorities.
For more tips on how to protect your family from cyber bullying, drop us a note on Facebook (facebook.com/nerdsoncall).

About The Author: Andrea Eldridge is CEO and co-founder of Nerds On Call, a computer repair company that specializes in on-site and online service for homes and businesses. Andrea is the writer of a weekly column, Nerd Chick Adventures in The Record Searchlight. She prepares TV segments for and appears regularly on CBS, CW and FOX on shows such as Good Day Sacramento, More Good Day Portland, and CBS 13 News, offering viewers technology and lifestyle tips. See Andrea in action at callnerds.com/andrea/.