Video Transcript
Heather: Now he is going to break down the things that you need to do today, to protect yourself from viruses, hackers and thieves — really important information.
Ted: Well it is Tech Tuesday, and today we’re talking about protecting your home computer from viruses, hackers and online criminals. Ryan Eldridge from callnerds.com, the co-founder, is with us here. And the first thing we want to talk, you’ve got three basic steps that everybody should be doing. The first one is something that I always kind of ignore, and that is update, right?
Ryan: Yeah.
Ted: You’ve got to update when there is one available.
Ryan: We’ve got to update our operating system. Windows 10 just finally finished its free roll out, so now you have to pay for it. So, everybody’s kind of complaining, “I don’t want to go to Windows 10. I’m happy with 7,” or, “I’m happy with 8” or whatever. But the thing is, if you’re running an older operating system you are vulnerable to viruses and spyware. These guys have had years to just practice what they want to do to your operating system and just damage it, and get in there and do stuff. So, update your operating system.
And today it happens to be the rollout of the new Windows 10 anniversary edition. It’s kind of fancy speak for their first service pack. We always say, tell everybody, “Just hold off on installing a new operating system until their first service pack comes out.” But now that the new anniversary edition is out, its adding some new functionality, its adding new security software updates to it. So you even have new things like, Cortana is going to be a little bit better, there’s a better Start menu where it’s going to be a little more intuitive. When you click on an item, like a news item in the Start menu, it will take you directly to the story rather than just opening the news app. There’s a new integration for the stylists, Windows Ink, so all kinds of new stuff.
Ted: Right.
Ryan: And they promise they’re not going to break anything. I know that’s one of the things we’re always worried about as we get a new operating system. Our new update, it’s going to break something, or we’re not going to be used to using it, and everything’s going to move around. Well, Windows 10 is supposed to unify their ecosystem and make it just a little easier for you to get around from your phone, to your Xbox, to your PC.
Ted: Right, so the idea that what I do is I ignore it and I don’t do it because I want to be safe, that’s actually the wrong thing because I am not protecting myself. Number two, what’s number two?
Ryan: Number two, well, update your anti-virus. A lot of us buy a brand new PC and we get some freeware on there. We’ve got Norton or McAfee or something, and we think we’re protected. Well, about 90 days after we open up the PC that expires, and we are no longer being protected.
Ted: So that does work, because I think I’m wasting my money with this Norton or this McAfee or this and that.
Ryan: Yeah, Windows has its own version. This like Windows Defender or something like that, and it’s okay, or Microsoft Security Essentials, something like that. It’s okay, but it’s not as good as a dedicated antivirus system. We use OpenText in our company and it is awesome, because it is looking at not just the names of files that get infected, its looking at the behavior of the virus itself. And so, even if the world doesn’t know that it’s a virus yet it can go in and attack it and remove it, and it just keeps you a lot safer. And it doesn’t take a lot of space, there’s not a lot of time for scanning, it’s just an awesome little product.
Ted: All right. Number three, our last tip for the day?
Ryan: Yeah, Lastly you want to back-up your system. We are always being told, “Back-up, back-up back-up,” and then we never do it.
Ted: Yes
Ryan: And you want to really have three basic back-ups. You want to have iCloud, or some kind of cloud back-up. There I go, I switched to Apple, but some kind of Apple… I am going to mess up. Some kind of cloud back-up, but also some kind of back-up that you have near your computer like an…
Together: External drive.
Ryan: External hard drive, or something like that. And you want to make sure that it’s versioning, because if you just back-up everything on your system, you are going to be backing-up files you don’t need, and all kinds of stuff. What you want to do is find which version….
Ted: …find what you want and put it on a [inaudible 0:03:21.4] drive or something like that.
Ryan: Yeah, and you want it versioned because that way if you get infected you can go back to the day before your infection, and you’re back to normal. You don’t have to go through this whole restore period.
Ted: All right.
Ryan: It makes sense?
Ted: It makes perfect sense. Now I need to go do it. All right, Ryan Eldridge from nerds on call, Thank you.
Ryan: You’re welcome.
Ted: Heather?
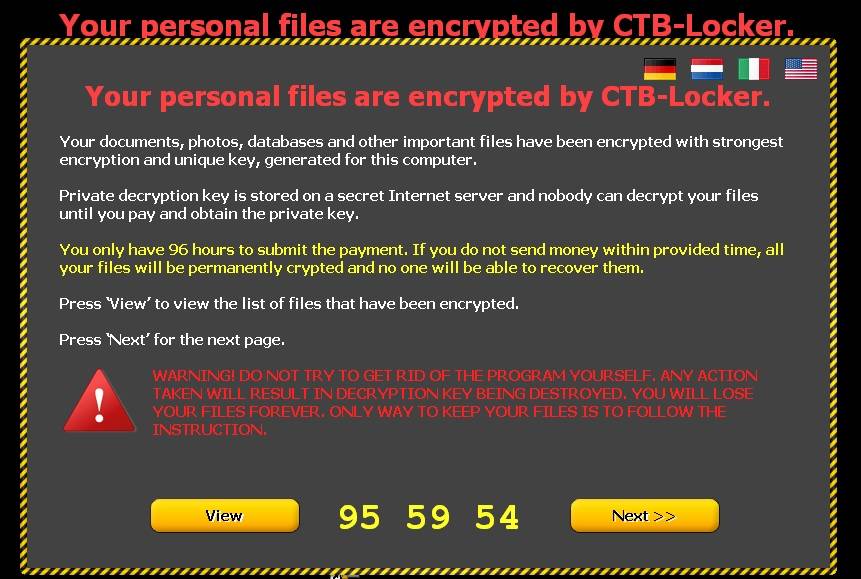
Even the most savvy of internet users might have trouble defining what exactly ransomware is. Ransomware is very similar to malware in the sense that it gets onto your computer like a virus. Once there is ransomware on your system, the parasitic code encrypts your files, making them inaccessible to you. In order to regain control of your data, you must purchase the decryption key from the criminal who infected your system in the first place. These criminals usually force victims to pay with bitcoins, an untraceable online currency. If you are curious, the cost of getting your data back after a ransomware attack averages around $500, but there have been cases in which victims pay much, much more.
Earlier in February, the Hollywood Presbyterian Medical Center was extorted for $17,000 after their data was locked during a ransomware attack. During the time the system was encrypted, hospital workers were locked out of certain computers that were necessary for day to day tasks, and electronic communications systems were disabled, forcing the medical center’s communication flow to suffer greatly. Even in such a large scale ransomware attack, the FBI stated that if you need your data back from the criminals, the only way to get it is by paying the ransom.
Ransomware is becoming more and more common, and attacks are on the rise. McAfee Lab researchers saw more than 4 million incidents of ransomware in the 2nd quarter of 2015 alone. With the recent boom in virtual payment methods, criminals are able to extort payments through new mediums while still remaining anonymous. For online criminals, the ransomware business is quite lucrative.
The most common means of your computer being infected with ransomware is through malicious email attachments; although drive-by downloads from compromised websites is also a leading cause. The vast majority of websites that are infected are sites with adult content. With the ability to spoof links, criminals can make a link seem like it leads to a legitimate site, but it could lead you somewhere that is infected. Adobe Flash Player is the lead tool for spreading infections because the program is used to auto-play videos and graphics on popular websites. Criminals exploit vulnerabilities in Flash Player and make it so that once the site is visited, the script runs automatically and the infectious content begins to be written.
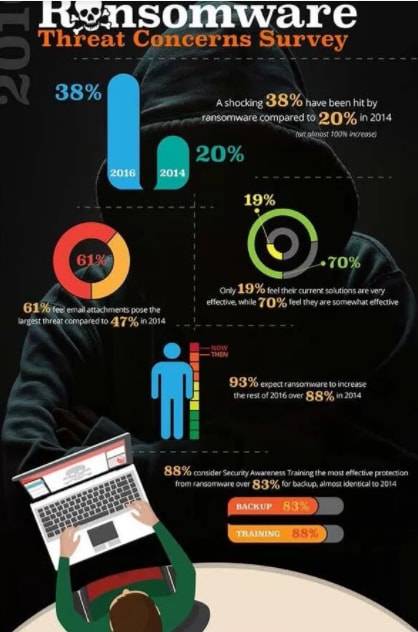
To avoid falling victim to any ransomware demands, be sure to maintain an up-to-date, reliable data backup. Ideally, you should have a backup on your hard drive, as well as an off-site backup ready to go in cloud storage. If you make sure to set automatic backups, and that the software you use includes a versioning option so that you can maintain historical data points, you only need to wipe your hard drive and restore a backup from before your device was infected. A few simple steps can really make all the difference in avoiding or recovering from a ransomware attack.
If you are hoping to reduce the likelihood that you will get infected with ransomware, there are a handful of precautionary measures you can take. Obviously, avoid opening suspicious attachments or clicking links from an unsolicited email or social media posting. Be sure you keep your Malware detection software up-to-date as well as your operating system, web browsers, and Adobe Flash Player to avoid any vulnerabilities. It also helps to disable the auto-play feature of Flash in your web browser so that you will be prompted before Flash Player runs on any page. For a good lesson on how to disable auto-play, check out How to Geek’s tutorial.
Nerds on Call has partnered with industry leader IDrive to protect your files, photos, and videos: Get 5TB of Cloud Storage for just $8/mo or 50% off your first year!
Get IDrive here – or contact us and one of our Nerds will set up data backup for you.
Like This? We have more!
Sign up below to be kept in the loop and be sent more content like this in the future!
About The Author: Andrea Eldridge is CEO and co-founder of Nerds On Call, a computer repair company that specializes in on-site and online service for homes and businesses. Andrea is the writer of a weekly column, Nerd Chick Adventures in The Record Searchlight. She prepares TV segments for and appears regularly on CBS, CW and FOX on shows such as Good Day Sacramento, More Good Day Portland, and CBS 13 News, offering viewers technology and lifestyle tips. See Andrea in action at callnerds.com/andrea/.