There’s a new and nasty “ransomware” virus called CryptoLocker sweeping the web, taking computers hostage and demanding that users pay an exorbitant “ransom” to get their data back. Here’s what you need to know to avoid becoming a victim of this malicious software.
Ransomware is the term adopted by those in the tech industry to describe malware that infects a computer and then demands a fee to reverse its own ill effects. CryptoLocker is spread most commonly through an infected email attachment, though it can be imbedded in hacked or malicious websites. Users that happen upon the compromised site will be vulnerable to infection if they have out of date browser plug-ins, which the virus has been known to exploit.
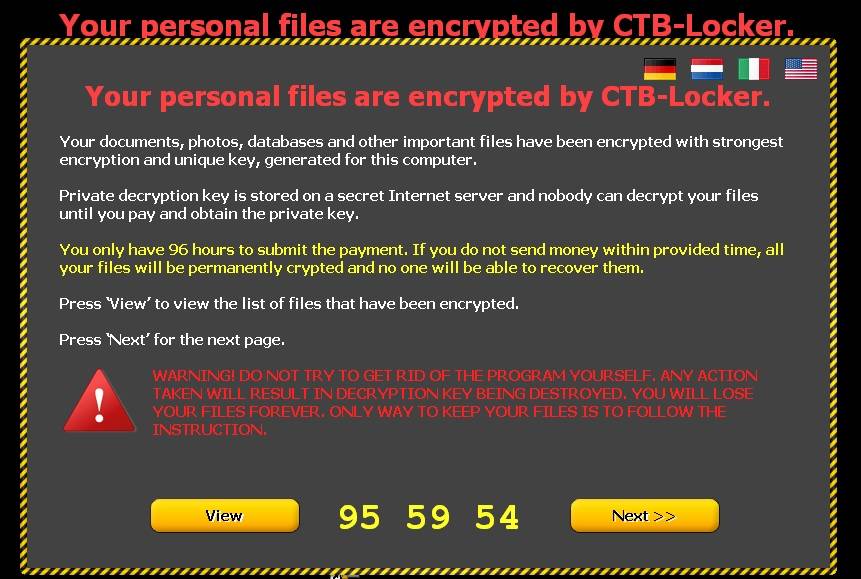
Upon infecting a computer, CryptoLocker often shows no outward signs of its presence for hours or even days. During this time the virus encrypts all of the files stored on the PC, making data unusable. Once the encryption process is complete, a popup message appears on the infected PC’s screen notifying the user that all of their files have been encrypted and demanding $300 for a “private key” to decrypt the data. A countdown timer gives the user 3 days to pay before the “private key” is destroyed. Recent reports have indicated that perpetrators will also offer an “overdue ransom” option to victims, demanding about $2,000 from those who don’t pay within the original demand window.
While the virus itself is relatively easy to remove, compromised data is unable to be read until it’s decrypted, a process that is only possible with a decryption key. This leaves most victims stuck either paying the ransom or giving up their data. Payments are channeled through Bitcoins, an online currency that doesn’t travel through banks but instead through encrypted web-based transactions, making them nearly impossible to trace.
Many victims attempt to remove the virus, assuming that their data will return to normal when the virus has been purged from their system. Unfortunately, removing the virus serves only to break the payment chain, leaving many users with no way to pay the ransom should they determine that it’s worth $300 to decrypt their files. This has led perpetrators to establish an independent online “CryptoLocker Decryption Service” website where victims can go to pay their ransom and retrieve their decryption code.
To reduce the likelihood that you’ll become infected with CryptoLocker, make sure that you keep anti-virus and anti-malware programs up to date and review the program’s settings to ensure that automatic updating is enabled. Download and install all updates to your Operating System and browser (most commonly Internet Explorer, Chrome, Firefox or Safari).
Review the browser plug-ins you have installed (like Java and Adobe) and visit each software company’s website to install the most up-to-date version of browser plug-ins. Avoid opening email attachments unless you are expecting the file and trust the original sender.
While establishing a reliable data backup can be invaluable in retrieving lost data, keep in mind that CryptoLocker can attack any files accessed through an infected PC, including USB-linked storage devices, external hard drives, even cloud-based backup accounts if they’re mapped to a drive letter on the infected machine. Files accessed over VPN from an infected computer can be compromised.
While cloud backup is one of the best options to protect your data from CryptoLocker, if your data auto-syncs then the encrypted files will replace the good files stored in your cloud account. If you utilize auto-sync, make sure that your cloud backup provider offers “versioning” (which allows you to retrieve an older version of a synced document) and that, if necessary, you activate the feature prior to infection.
Losing your photos, videos or files is a nightmare. Don’t lose sleep worrying about data loss. Get 5TB of Cloud Storage for just $8/mo or 50% off your first year!
Learn more about IDrive here – or contact us and one of our Nerds will get it set up for you.

About The Author: Andrea Eldridge is CEO and co-founder of Nerds On Call, a computer repair company that specializes in on-site and online service for homes and businesses. Andrea is the writer of a weekly column, Nerd Chick Adventures in The Record Searchlight. She prepares TV segments for and appears regularly on CBS, CW and FOX on shows such as Good Day Sacramento, More Good Day Portland, and CBS 13 News, offering viewers technology and lifestyle tips. See Andrea in action at callnerds.com/andrea/.