I never thought I’d look back fondly on the days when malware just caused annoying pop-ups. The newest bug crawling the Web is called “ransomware,” and it holds your computer hostage until you pay a demanded ransom. The latest has several names: FBI Moneypak, Citadel Reveton or simply, Reveton Virus.
The Internet Crime Complaint Center (IC3) is the result of a partnership between the FBI and the National White Collar Crime Center. Designed to give cybercrime victims an easy way to report crimes, they also assist law enforcement in obtaining evidence to prosecute culprits. The IC3 first began receiving complaints about Reveton Ransomware in 2011. They issued a warning about it on their website in May 2012. Today, the IC3 receives dozens of complaints each day from all over the world.
Most viruses activate after opening a file or attachment. Reveton is particularly insidious because it can install itself when a user simply clicks on a compromised website. It then locks down the computer by encrypting files on the hard drive or producing an inescapable black screen. A message is displayed directing the user to a bogus FBI, Department of Justice or IC3 website. The user is accused of a variety of Internet crimes, from illegal downloading of copyrighted materials to possession of child pornography.
There are a multitude of variants of the malware, but in all cases, the user is instructed to pay a penalty fine in order to unlock the computer, typically $100-200. Most versions demand that payment is made with pre-paid credit card, such as a Moneypak card (sold at Walgreens or Wal-mart) or an”Ultimate Game Card” which are no longer sold.
Some variants of the virus turn on the computer’s webcam, recording video and displaying images back to the victim as an additional “we know who you are” scare tactic. Others disable current anti-malware and antivirus software. Once users have paid the “fines” or clicked through the warning message to investigate, it gets worse. The virus remains in the background, sending personal information to the hackers to be used in further crime, such as identity theft and capturing of credit card numbers or financial information.

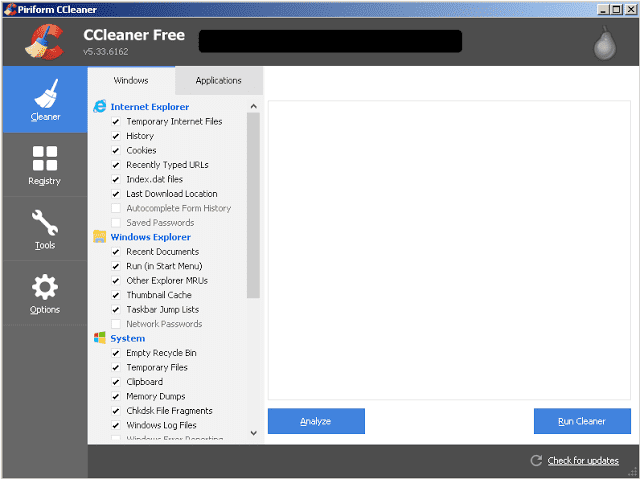
While you certainly should NOT pay any “fine” demanded by the bogus malware, what should you do if you’re infected with Reveton Ransomware? The answer depends on how much control you maintain over your computer. If you’re able to access the Internet, download Malwarebytes. They’ve kept up with variants as the malware has adapted and evolved, making it a strong contender to remove all versions from your computer.
Some victims are completely locked out of their system, unable to access the Internet or their desktop. The IC3 and the FBI recommend that these users contact a computer repair specialist. They warn potential victims that even if they’re able to unfreeze their system, the malware “may still operate in the background” and “certain types of malware have been known to capture personal information such as usernames, passwords, and credit card numbers through embedded keystroke logging programs.” (www.fbi.gov/news/stories/2012/august/new-internet-scam)
If you’re feeling confident and want to try some DIY options, repair suggestions are detailed here. Just keep in mind that many are advanced, may lead to data loss or operating system damage, and there’s no guarantee that the virus won’t continue to run in the background as the IC3 warns.
If you haven’t been attacked by this nasty bug, make sure that your system’s malware protection is up to date, downloading updates and running scans regularly. Consider installing a firewall router to limit unauthorized, outward-bound traffic from your computer to the Internet and limit your surfing to lesser-known sites, particularly those that facilitate file sharing.
Nerds On Call Computer Repair is the best in-shop, onsite and online computer repair company in Sacramento, CA. We’ve served Sacramento County and surrounding areas since 2004! Nerds offers same day computer repair for both hardware and software issues on both Apple & PC laptops and desktops computers. Our Nerd computer technicians work hard to make your computer repair experience as quick & pleasant as possible. Visit our Sacramento computer repair service page here: https://callnerds.com/computer-repair-sacramento/. Or call us now at 1-800-919-6373 to set up a same day appointment.